Category: Paloalto Firewall

Palo Alto Firewall Command Line Reference
Palo Alto Firewall Command Line Reference

Reset Paloalto Firewall Interface to Default State of Not Configured
To reset unused PaloAlto firewall interface to its default state of not configured, choose the interface and press delete option at the bottom.
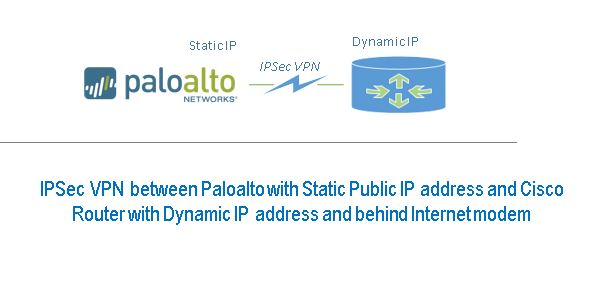
Configure Site to Site IPSec VPN Tunnel between Cisco Router and Paloalto Firewall
One end of IPSec tunnel is a Paloalto Firewall with Static Public IP address and the other end is Cisco router with Dynamic IP address…

Monitor Paloalto with OpManager
Step 1 – Configure SNMP in Paloalto Firewall Note: Paloalto Firewall supports SNMP version v2c and v3 and not v1. Configure SNMP Community String Login…

Configure Paloalto Firewall to access External Dynamic List – Series II
Series II Configure Paloalto Firewall to access External Dynamic List We are assuming that your feed server is running on your local network and the…

Setup your own IP Feed in your LAN – Series I
Series I Firewall Feed is an open source web based tool written on PHP to setup and manage your own IP address feed in your local…

Challenges upgrading Paloalto firewall to 8.1.0 Version
We were upgrading all paloalto firewall appliances to latest base version 8.1.0 and we encountered numerous issues. We are sharing our experience here, you may…

Configure IKEV1 Site to Site VPN between Cisco ASA and Paloalto Firewall
In this guide, we are configuring IKEV1 VPN between Cisco ASA and Paloalto firewall. This is applicable to all models of Cisco and PA firewalls.…